
Conceal’s mission is to stop ransomware and credential theft for companies of all sizes by developing innovative solutions that provide social engineering protection in any browser ensuring employee productivity and data protection.
ConcealBrowse, powered by the advanced SherpaAI engine, stands at the forefront of AI-driven browser security. By seamlessly merging real-time threat analysis with user experience, we provide dynamic protection, pre-emptively tackling cyber intrusions. ConcealBrowse isn’t just a tool—it’s a comprehensive solution.
The ConcealBrowse team specializes in assisting businesses with planning for and strategizing how best to deploy and optimize ConcealBrowse’s myriad features. From AI-powered dynamic browser isolation using VPNs to contextual analysis, Conceal guide you through best practices, ensuring your browser environment remains secure yet user-friendly.
Beyond its core capabilities, the ConcealBrowse service extends to consulting on licenses, understanding telemetry data integration for tools like Splunk and Elasticsearch, and maximizing its proactive defence strategies. For a tailored approach to your browser security, reach out to Conceal and Kompingo, to experience how ConcealBrowse can revolutionize your digital safety. Enhanced visibility, empowered users, and financial efficiency are within your reach.
Proactively Detect and Prevent Threats
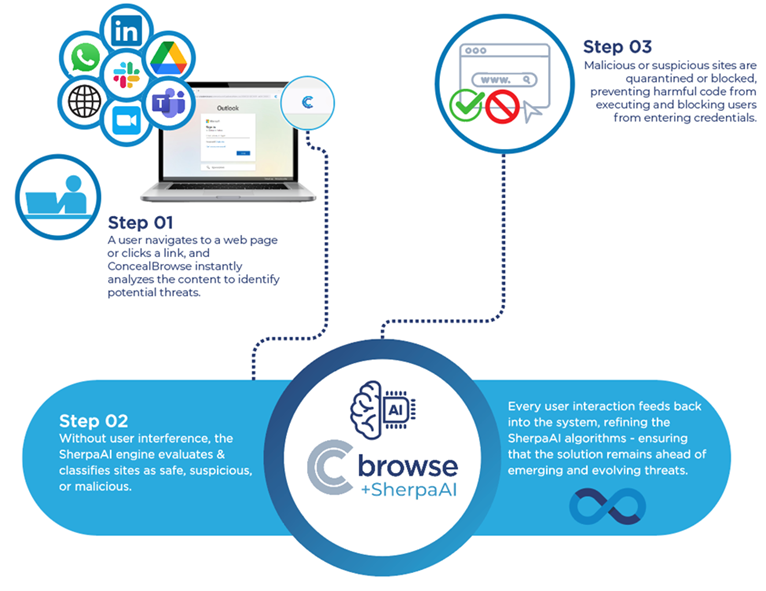
ConcealBrowse intuitively gauges risky internet traffic and determines one of three routes: allow known ‘good’ URLs to continue their normal path, block known malicious content in its tracks, or route suspicious or unknown traffic activity through our dynamic software-defined network and isolation environments to remove context and provide extra layers of privacy and security to users and enterprises.
ConcealBrowse acts as the brain to make proactive decisions about the security risk associated with internet use and automatically prevents risky transactions — seamlessly without user interruption. Browsing activity takes place in the isolated environment, ensuring that any malicious codes or files never execute on your enterprise’s devices.
Benefit from these key features:
- Automatically detects risky internet activity
- Proactively prevents your network from compromise
- Reduces expenses on detection, prevention and response